Critical Infrastructure Security: Safeguarding Essential Services
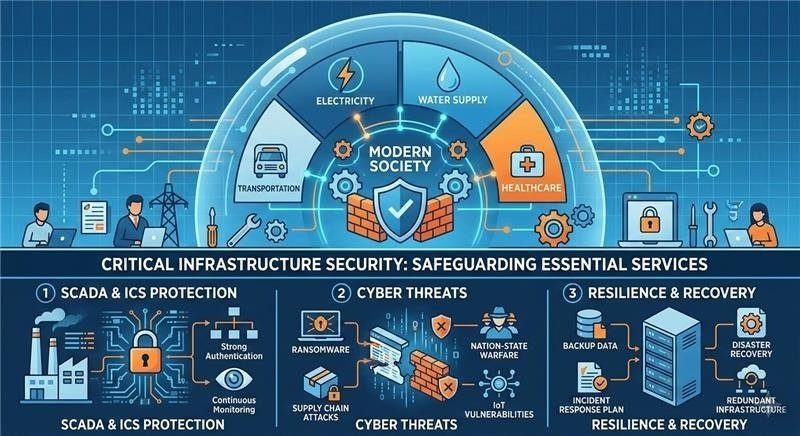
Modern societies depend heavily on critical infrastructure systems that provide essential services such as electricity, water supply, transportation, and healthcare. These systems form the backbone of national economies and public safety. However, with increasing digitalization and connectivity, these infrastructures have become attractive targets for cyberattacks.
Critical Infrastructure Security focuses on protecting these essential systems from cyber threats, technical failures, and physical disruptions. Governments and organizations worldwide are investing heavily in security frameworks to ensure the reliability and resilience of these vital services.
Why Critical Infrastructure Security Is Important
Critical infrastructure supports everyday life. Power grids deliver electricity to homes, water systems provide clean drinking water, transportation networks move people and goods, and healthcare systems save lives. A successful cyberattack on any of these sectors can cause severe disruptions.
For example, a cyberattack on a power grid could lead to widespread blackouts. Similarly, a compromised hospital system could delay medical treatments and affect patient care. Such incidents can impact national security, economic stability, and public safety.
Because many infrastructure systems are now connected to digital networks, attackers can exploit vulnerabilities to gain unauthorized access. Therefore, implementing strong cybersecurity measures is crucial for preventing disruptions and ensuring continuous operation.
Key Components of Critical Infrastructure Security
1. SCADA System Security
Supervisory Control and Data Acquisition (SCADA) systems are widely used to monitor and control industrial processes in sectors like energy, water management, and manufacturing.
SCADA systems collect real-time data from sensors and devices and allow operators to manage infrastructure remotely. While this improves efficiency, it also introduces cybersecurity risks.
To secure SCADA systems, organizations implement measures such as:
- Network segmentation
- Strong authentication protocols
- Continuous monitoring of system activity
- Secure communication channels
Protecting SCADA systems is essential because they control critical operations such as electricity distribution, water treatment plants, and oil pipelines.
2. Industrial Control System (ICS) Protection
Industrial Control Systems (ICS) are the technologies used to control industrial processes and machinery. They are commonly used in power plants, manufacturing facilities, and transportation systems.
Historically, ICS environments were isolated from external networks. However, modern infrastructure increasingly connects these systems to corporate networks and cloud platforms for better efficiency and remote management.
This connectivity creates new security challenges. To protect ICS environments, organizations should implement:
- Strict access control policies
- Regular system updates and patch management
- Intrusion detection systems
- Employee cybersecurity training
By strengthening ICS security, organizations can prevent unauthorized access that could manipulate industrial operations.
3. Backup and Disaster Recovery
Even with strong defenses, cyber incidents or technical failures can still occur. This is why backup and disaster recovery strategies are critical for infrastructure security.
Backup systems ensure that important data and configurations can be restored if systems are compromised. Disaster recovery plans help organizations quickly restore operations after disruptions.
Key elements of effective disaster recovery include:
- Regular system backups
- Redundant infrastructure and failover systems
- Incident response plans
- Periodic recovery testing
For critical infrastructure, downtime can have serious consequences. A well-prepared disaster recovery strategy ensures services can be restored quickly and safely.
Emerging Threats to Critical Infrastructure
As technology evolves, so do the threats facing infrastructure systems. Some emerging risks include:
Ransomware Attacks: Attackers encrypt systems and demand payment to restore access.
Supply Chain Attacks: Cybercriminals exploit vulnerabilities in third-party vendors or software providers.
Nation-State Cyber Warfare: Some attacks target infrastructure systems to disrupt national stability.
IoT Vulnerabilities: Connected devices in smart grids and smart cities can introduce new security weaknesses.
These threats highlight the importance of proactive security strategies and continuous monitoring.
Best Practices for Strengthening Infrastructure Security
Organizations responsible for critical infrastructure should adopt a multi-layered security approach. Key best practices include:
- Implementing network segmentation for operational systems
- Monitoring systems with advanced threat detection tools
- Conducting regular security audits and vulnerability assessments
- Training staff on cybersecurity awareness
- Establishing strong incident response plans
Collaboration between governments, private companies, and security experts is also essential to address evolving threats.