Network Security: Protecting Digital Communication in a Connected World
In today’s digital era, organizations rely heavily on computer networks to communicate, share data, and run business operations. Whether it is sending emails, accessing cloud services, or managing enterprise systems, networks play a crucial role in everyday digital activities. However, as networks grow larger and more complex, they also become prime targets for cybercriminals.
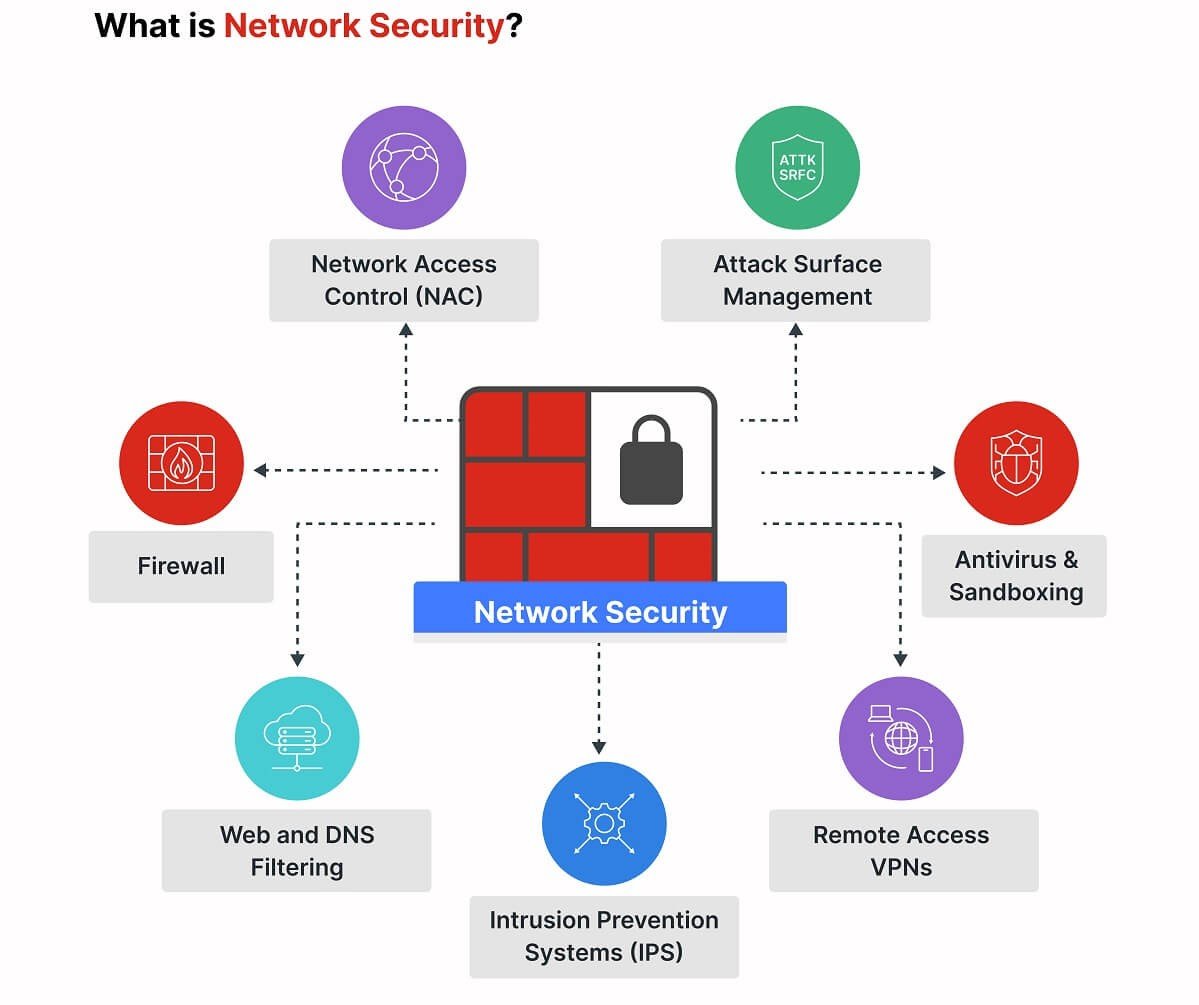
Network Security focuses on protecting both internal and external network communications from unauthorized access, cyberattacks, and data breaches. It involves implementing various technologies, policies, and practices to ensure that data transmitted across networks remains secure and reliable.
Without strong network security measures, attackers may intercept data, disrupt services, or gain access to sensitive systems.
Why Network Security Is Important
Organizations today operate in highly interconnected environments where employees, partners, and customers access networks from multiple devices and locations. While this connectivity increases productivity, it also expands the attack surface for cyber threats.
Cybercriminals often target networks to steal sensitive information, install malware, or disrupt operations. Common threats include hacking attempts, phishing attacks, ransomware, and distributed denial-of-service (DDoS) attacks.
Strong network security helps organizations:
- Protect confidential data during transmission
- Prevent unauthorized access to systems
- Detect and respond to cyber threats quickly
- Ensure business continuity and system availability
- Maintain compliance with cybersecurity regulations
By securing networks, businesses can safeguard critical information and maintain trust with customers and partners.
Key Components of Network Security
1. Firewalls
A firewall acts as the first line of defense in network security. It monitors incoming and outgoing network traffic and blocks suspicious or unauthorized connections based on predefined security rules.
Firewalls can be hardware-based, software-based, or cloud-based. They help prevent attackers from gaining access to internal networks while allowing legitimate communication to continue.
Modern firewalls also include advanced capabilities such as:
- Application-level filtering
- Threat detection and prevention
- Traffic monitoring and logging
- Intrusion prevention features
Firewalls play a critical role in protecting networks from external threats.
2. Intrusion Detection and Prevention Systems (IDS/IPS)
Intrusion Detection Systems (IDS) and Intrusion Prevention Systems (IPS) are security technologies used to detect and respond to suspicious network activity.
An IDS monitors network traffic and alerts administrators if unusual behavior or potential threats are detected. An IPS goes one step further by automatically blocking malicious activity in real time.
These systems analyze network traffic patterns to identify threats such as:
- Malware communication
- Unauthorized access attempts
- Suspicious data transfers
- Exploits targeting vulnerabilities
Using IDS/IPS solutions helps organizations detect attacks early and respond before significant damage occurs.
3. Network Segmentation
Network segmentation divides a large network into smaller, isolated segments to improve security and performance. By separating different systems or departments into individual network zones, organizations can limit the spread of cyber threats.
For example, sensitive systems such as financial databases or internal servers can be placed in restricted network segments with stricter access controls.
Benefits of network segmentation include:
- Reduced risk of lateral movement by attackers
- Better control over network traffic
- Improved monitoring and security management
- Enhanced protection for critical systems
Segmentation ensures that even if one part of the network is compromised, attackers cannot easily access the entire network.
4. Secure Wi-Fi and VPNs
Wireless networks are convenient but can also introduce security risks if not properly protected. Unsecured Wi-Fi networks allow attackers to intercept data or gain unauthorized access.
To improve wireless security, organizations should implement:
- Strong encryption protocols (such as WPA3)
- Secure authentication mechanisms
- Regular network monitoring
Virtual Private Networks (VPNs) provide another layer of security by encrypting internet connections. VPNs create secure tunnels between devices and networks, allowing remote users to safely access corporate resources.
VPNs are especially important for remote work environments where employees access company systems from different locations.
Common Network Security Threats
Networks face a variety of cyber threats that can compromise security and disrupt operations. Some of the most common threats include:
Malware Attacks
Malicious software spreads across networks to steal data or damage systems.
DDoS Attacks
Attackers overwhelm networks with massive traffic to make services unavailable.
Man-in-the-Middle Attacks
Hackers intercept communication between two parties to steal sensitive information.
Unauthorized Access
Weak authentication systems allow attackers to gain access to internal networks.
Understanding these threats helps organizations build stronger defenses.
Best Practices for Strengthening Network Security
To protect networks effectively, organizations should adopt multiple security layers. Important best practices include:
- Implement strong firewall policies
- Use intrusion detection and prevention systems
- Segment networks to isolate critical systems
- Secure wireless networks and enable encryption
- Use VPNs for remote access
- Monitor network traffic continuously
- Conduct regular security audits and vulnerability assessments
Combining these strategies creates a robust network security framework.