Database Security in 2026: Protecting Data from Unauthorized Access, Theft, and Corruption
In today’s data-driven digital world, databases are the foundation of almost every business system. From customer information and financial records to healthcare data and business intelligence, databases store highly sensitive and mission-critical information. As cyber threats continue to evolve, database security has become one of the most important pillars of cybersecurity.
Database security focuses on protecting databases from unauthorized access, data theft, corruption, misuse, and service disruption. Whether an organization uses SQL databases, NoSQL platforms, or cloud-managed database services, securing stored data is essential for business continuity and customer trust.
One of the most significant threats in this area is SQL injection.
SQL injection remains one of the most common and dangerous database attacks even today. Attackers exploit vulnerable input fields such as login forms, search boxes, or URL parameters to inject malicious SQL commands into database queries. If applications fail to properly validate user input, attackers may gain unauthorized access to entire databases, steal confidential information, modify records, or even delete critical data. Recent cybersecurity reports confirm that SQL injection is still a major cause of data breaches in modern applications.
The best way to prevent SQL injection is through parameterized queries, prepared statements, input validation, and secure coding practices. Modern development frameworks increasingly integrate built-in protections, but developers must still follow secure database query standards.
Another key area of database security is role-based access control (RBAC).
RBAC ensures that users only have access to the data and functions required for their job roles. For example, a finance manager may access billing data, while customer support teams may only view limited customer records. This principle is known as least privilege access, and it significantly reduces the risk of insider threats and accidental data exposure.
Today, businesses are moving beyond simple user-permission models toward dynamic identity-driven access systems. RBAC has become a critical trend because hybrid work environments and cloud applications require stronger identity governance.
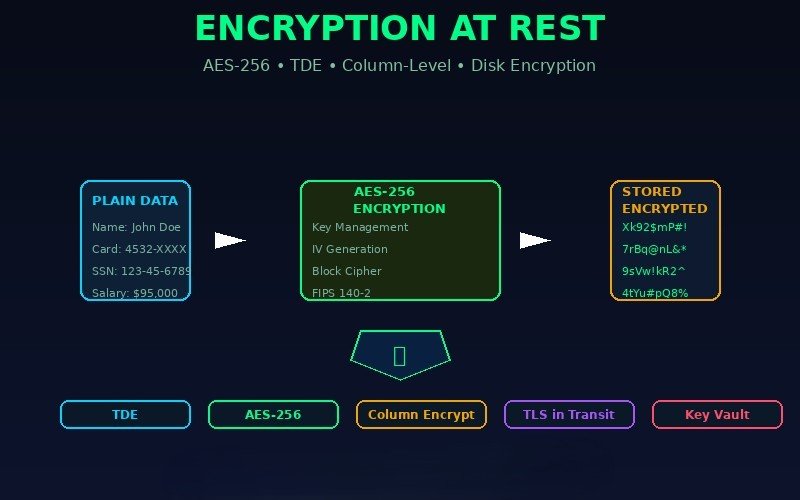
Another major trend in 2026 is encryption of data at rest.
Data at rest refers to information stored in database files, backups, servers, and cloud storage. Encrypting this data ensures that even if attackers gain physical or logical access to the storage system, the data remains unreadable without the correct decryption keys.
Technologies such as Transparent Data Encryption (TDE), disk-level encryption, and column-level encryption are widely used to protect sensitive fields like passwords, payment information, and personal records. Many organizations now combine encryption at rest with TLS encryption for data in transit to achieve full lifecycle data protection.
Database monitoring is also becoming increasingly important.
Modern security tools continuously monitor database activity logs, access attempts, query behavior, and abnormal data requests. AI-powered monitoring systems can detect suspicious activities such as repeated failed login attempts, unusual query patterns, or unexpected data exports in real time.
This proactive approach helps organizations identify threats early and reduce the risk of large-scale breaches.
Another growing focus is backup and recovery protection.
Even the most secure databases must prepare for ransomware attacks, accidental corruption, or system failures. Secure backups, encrypted replicas, and disaster recovery strategies help ensure data availability and fast restoration.
Looking ahead, database security is moving toward zero trust data access, AI-driven anomaly detection, and privacy-first encryption models.
In a world where data is one of the most valuable assets, protecting databases is no longer optional — it is essential for business resilience, compliance, and trust.