In today’s hyper-connected digital landscape, network security has become the backbone of organizational cybersecurity. As businesses rely heavily on cloud services, remote work, and interconnected systems, securing both internal and external network communications is more critical than ever. In 2026, network security is no longer just about defending perimeters—it’s about building resilient, adaptive systems that can withstand evolving cyber threats.
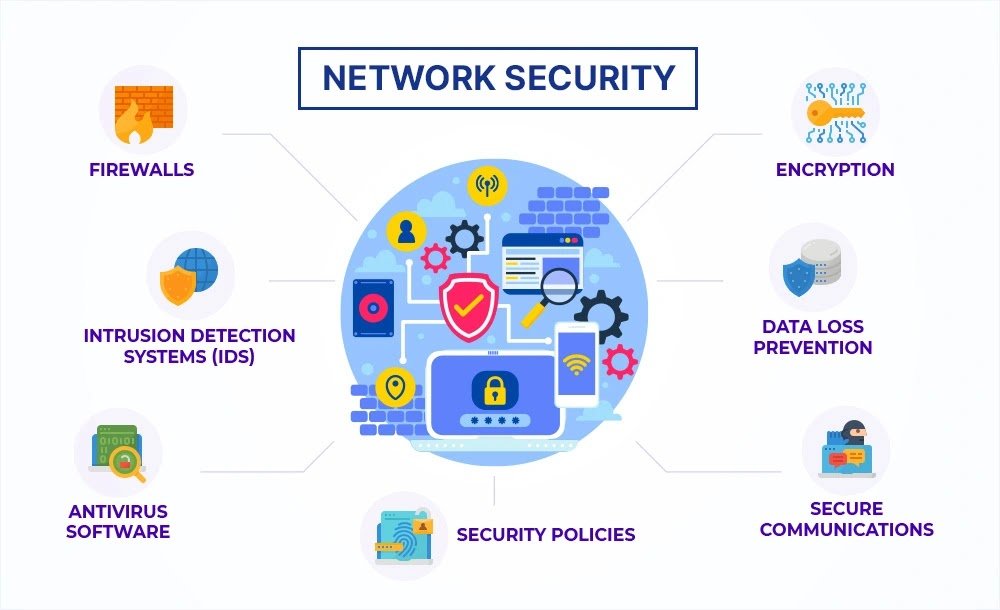
Network security refers to the strategies, technologies, and practices used to protect the integrity, confidentiality, and availability of data as it travels across networks. From small businesses to large enterprises, every organization must ensure that its networks are safeguarded against unauthorized access, misuse, and attacks.
Why Network Security Is Essential Today
Cybercriminals are constantly developing sophisticated methods to infiltrate networks. Attacks such as ransomware, phishing, and distributed denial-of-service (DDoS) can disrupt operations and compromise sensitive data. With the rise of hybrid work environments, employees accessing networks from various locations and devices have increased the risk exposure significantly.
A single vulnerability in a network can serve as a gateway for attackers, allowing them to move laterally across systems. This makes comprehensive network security strategies essential for preventing breaches and minimizing damage.
Firewalls: The First Line of Defense
Firewalls remain one of the most fundamental components of network security. They act as a barrier between trusted internal networks and untrusted external sources, monitoring and controlling incoming and outgoing traffic based on predefined rules.
Modern firewalls go beyond basic packet filtering. Next-generation firewalls (NGFWs) provide advanced features such as deep packet inspection, intrusion prevention, and application awareness. These capabilities help organizations detect and block malicious activity in real time.
Intrusion Detection and Prevention Systems (IDS/IPS)
While firewalls control traffic flow, Intrusion Detection Systems (IDS) and Intrusion Prevention Systems (IPS) actively monitor network activity for suspicious behavior. IDS alerts administrators when potential threats are detected, while IPS takes it a step further by automatically blocking or mitigating those threats.
These systems are essential for identifying advanced attacks that may bypass traditional defenses. By analyzing traffic patterns and signatures, IDS/IPS solutions provide an additional layer of protection.
Network Segmentation: Limiting the Blast Radius
Network segmentation involves dividing a network into smaller, isolated segments to reduce the spread of attacks. If an attacker gains access to one segment, segmentation prevents them from easily moving to other parts of the network.
This approach is particularly useful in protecting sensitive data and critical systems. For example, separating financial systems from general user networks ensures that even if one area is compromised, the most valuable assets remain secure.
Micro-segmentation, an advanced form of segmentation, provides even finer control by securing individual workloads or applications.
Secure Wi-Fi and VPNs: Protecting Remote Access
With remote work becoming the norm, secure connectivity has become a top priority. Unsecured Wi-Fi networks can expose users to risks such as data interception and man-in-the-middle attacks.
Organizations should implement strong Wi-Fi security protocols, such as WPA3 encryption, and ensure that default credentials are changed. Employees should also avoid using public Wi-Fi for sensitive activities unless connected through a Virtual Private Network (VPN).
VPNs encrypt internet traffic, creating a secure tunnel between the user and the network. This ensures that data remains protected even when accessed from untrusted environments.
The Shift Toward Zero Trust Architecture
Traditional network security models relied on perimeter-based defenses, assuming that everything inside the network could be trusted. However, this approach is no longer effective in today’s dynamic environments.
Zero Trust Architecture (ZTA) operates on the principle of “never trust, always verify.” Every user, device, and application must be authenticated and authorized before accessing network resources. Continuous monitoring and verification further enhance security.
Automation and AI in Network Security
Artificial intelligence (AI) and automation are playing an increasingly important role in network security. These technologies can analyze vast amounts of data to detect anomalies and respond to threats in real time.
Automated security systems reduce response times and help organizations stay ahead of attackers. By leveraging machine learning, security tools can adapt to new threats and improve over time.
Final Thoughts
Network security is a critical component of any cybersecurity strategy. As threats continue to evolve, organizations must adopt a proactive and layered approach to protect their networks. Combining firewalls, IDS/IPS, segmentation, secure connectivity, and modern frameworks like Zero Trust can significantly enhance security posture.
In 2026, the key to effective network security lies in continuous monitoring, adaptability, and a strong security culture. By investing in the right technologies and practices, organizations can safeguard their data and maintain trust in an increasingly connected world.