Network Security: Securing Digital Communication in a Connected World
In today’s hyper-connected digital environment, networks are the backbone of communication, business operations, cloud services, and remote work. From enterprise servers to employee laptops and mobile devices, everything relies on secure network connectivity.
As cyber threats continue to evolve, Network Security has become one of the most critical pillars of modern cybersecurity. It focuses on protecting both internal and external network communications from unauthorized access, attacks, and data breaches.
Without strong network protection, attackers can intercept data, spread malware, disrupt operations, and gain access to sensitive systems.
Why Network Security Is Important
Modern organizations operate in complex environments where networks connect:
- Employees and remote workers
- Cloud platforms and SaaS applications
- IoT devices and smart systems
- Data centers and branch offices
This interconnected structure creates multiple entry points for cybercriminals.
Common risks include:
- Data interception
- Unauthorized access
- Malware spread
- Ransomware attacks
- Service outages
A single network vulnerability can expose an entire organization.
Strong network security helps protect business continuity, customer trust, and sensitive data.
Key Components of Network Security
1. Firewalls
A firewall acts as the first line of defense between trusted internal networks and external internet traffic.
It monitors incoming and outgoing traffic based on predefined security rules.
Modern firewalls offer advanced features such as:
- Deep packet inspection
- Application filtering
- Traffic monitoring
- Threat prevention
- Access control policies
Firewalls help block malicious traffic before it reaches internal systems.
2. IDS/IPS (Intrusion Detection & Prevention Systems)
Intrusion Detection Systems (IDS) and Intrusion Prevention Systems (IPS) help identify suspicious network behavior.
IDS monitors network traffic and alerts administrators when threats are detected.
IPS goes a step further by automatically blocking malicious activity.
These tools detect:
- Port scanning
- Malware communication
- Brute-force login attempts
- Suspicious data transfers
They are essential for real-time threat detection.
3. Network Segmentation
Network segmentation divides a large network into smaller isolated sections.
For example:
- HR systems in one segment
- Finance servers in another
- Guest Wi-Fi in a separate zone
This reduces the risk of attackers moving laterally across the network.
Benefits include:
- Better access control
- Improved traffic management
- Reduced breach impact
- Easier threat isolation
Segmentation is especially important in enterprise and industrial networks.
4. Secure Wi-Fi and VPNs
Wireless networks are convenient but highly vulnerable if not properly secured.
Organizations should implement:
- WPA3 encryption
- Strong passwords
- Hidden SSIDs
- Access controls
For remote access, VPNs (Virtual Private Networks) are essential.
A VPN encrypts internet communication and creates a secure tunnel between the user and the corporate network.
VPNs are widely used for:
- Remote employees
- Secure branch connectivity
- Safe public Wi-Fi access
They help protect sensitive data from interception.
Common Network Security Threats
Networks face multiple modern threats:
Malware Attacks
Viruses, worms, and ransomware spread across connected systems.
DDoS Attacks
Attackers flood the network with traffic to disrupt services.
Man-in-the-Middle (MITM) Attacks
Hackers intercept communication between two endpoints.
Unauthorized Access
Weak passwords or misconfigured access rules.
Understanding these threats helps build stronger defenses.
Best Practices for Strong Network Security
Organizations should follow these best practices:
- Deploy advanced firewalls
- Use IDS/IPS monitoring tools
- Implement network segmentation
- Secure Wi-Fi with strong encryption
- Use VPNs for remote access
- Apply Zero Trust access controls
- Monitor logs continuously
- Perform vulnerability scans regularly
A layered security approach provides the best protection.
Future of Network Security
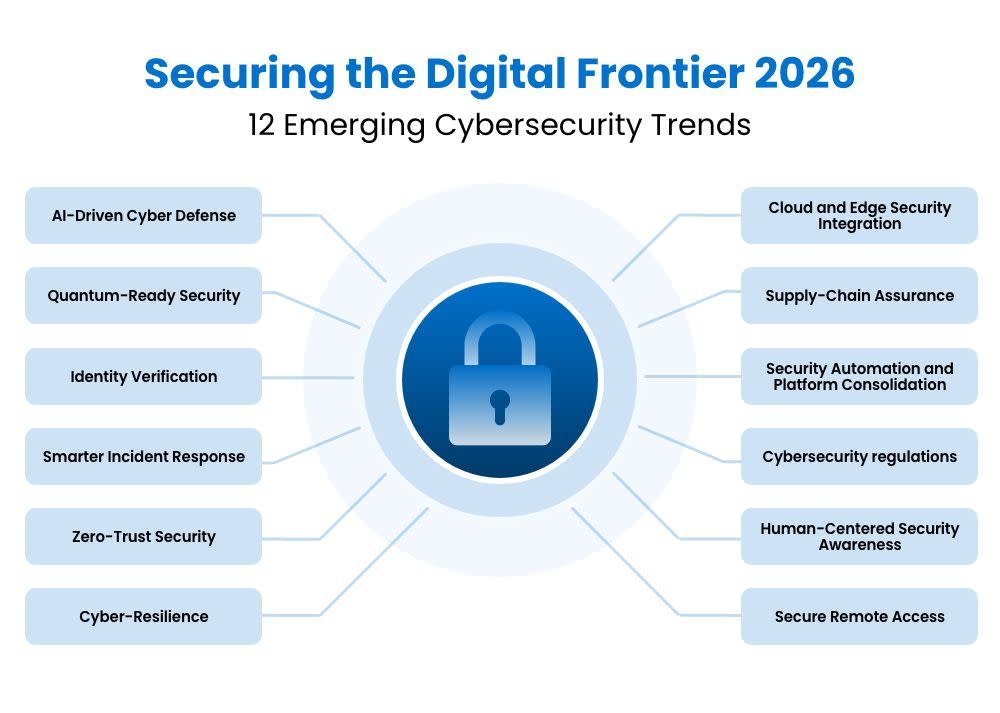
Network security is rapidly evolving with technologies such as:
- AI-powered threat detection
- Zero Trust Network Access (ZTNA)
- SASE (Secure Access Service Edge)
- Cloud-native network protection
These technologies are becoming essential as hybrid work and cloud networks continue to grow.