Database Security: Protecting Data from Unauthorized Access and Cyber Threats
In today’s digital world, data is one of the most valuable assets for organizations. Businesses store vast amounts of information in databases, including customer records, financial details, personal data, and operational information. Because of this, databases have become a major target for cybercriminals.
Database Security refers to the strategies, tools, and practices used to protect databases from unauthorized access, data theft, corruption, or misuse. It ensures that sensitive information remains secure, accessible only to authorized users, and protected from cyber threats.
Without proper database security measures, organizations risk data breaches, financial losses, legal penalties, and damage to their reputation.
Why Database Security Is Important
Modern applications rely heavily on databases to store and manage information. Databases power e-commerce platforms, banking systems, healthcare applications, and enterprise software. If attackers gain access to a database, they can steal or manipulate sensitive information.
Recent cyber incidents show that many data breaches occur because of weak security controls, poor access management, or vulnerabilities in applications interacting with databases.
Strong database security helps organizations:
- Protect sensitive business and customer data
- Prevent unauthorized access
- Maintain data integrity and accuracy
- Comply with data protection regulations
- Reduce the risk of cyberattacks and breaches
By implementing effective security practices, organizations can ensure that their databases remain safe from evolving cyber threats.
Key Components of Database Security
1. SQL Injection Prevention
One of the most common attacks targeting databases is SQL injection. This attack occurs when malicious code is inserted into database queries through application input fields.
For example, if a website does not properly validate user input, attackers may manipulate SQL queries to access confidential data, modify records, or even delete entire databases.
To prevent SQL injection attacks, developers should implement several security practices:
- Use prepared statements and parameterized queries
- Validate and sanitize all user inputs
- Avoid dynamic SQL queries when possible
- Use secure frameworks and libraries
- Implement Web Application Firewalls (WAF)
Preventing SQL injection is critical because even a single vulnerability can expose the entire database to attackers.
2. Role-Based Access Control (RBAC)
Not every user in an organization should have the same level of access to a database. Role-Based Access Control (RBAC) helps enforce the principle of least privilege by assigning permissions based on user roles.
For example:
- Database administrators may have full access to manage systems.
- Developers may have access only to development environments.
- Employees may only view limited data relevant to their roles.
RBAC improves security by ensuring that users can only access the information necessary for their responsibilities.
Key benefits of RBAC include:
- Reduced risk of insider threats
- Better control over user permissions
- Simplified access management
- Improved compliance with security policies
Organizations should regularly review access privileges and remove permissions that are no longer needed.
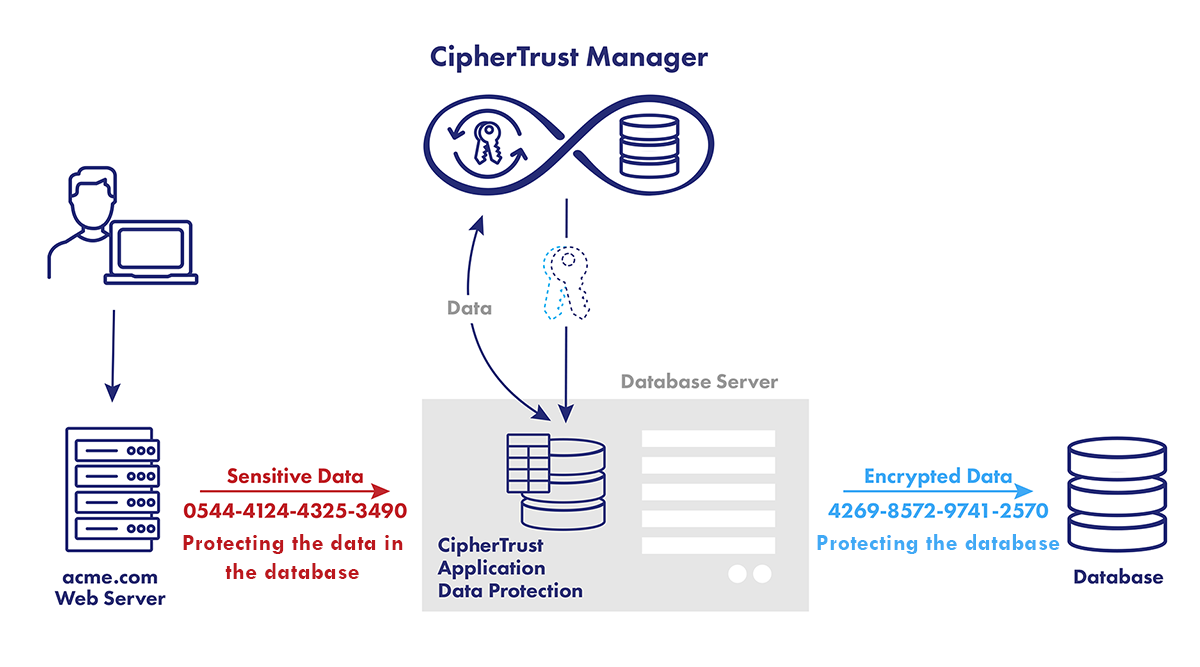
3. Encryption of Data at Rest
Encryption is a fundamental part of database security. Data at rest encryption protects stored data by converting it into unreadable code that can only be accessed with the correct encryption key.
If attackers gain access to encrypted databases, the data remains unusable without the decryption key.
Encryption is particularly important for protecting sensitive data such as:
- Personal identification information
- Financial records
- Health information
- Business confidential data
Modern database systems support built-in encryption mechanisms that help secure data stored in databases, backups, and storage devices.
Proper key management is also essential. Organizations must securely store and control encryption keys to prevent unauthorized access.
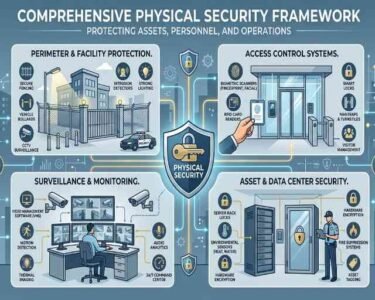
Additional Best Practices for Database Security
Beyond the core security methods, organizations should adopt additional strategies to strengthen database protection:
Regular Security Updates
Keeping database software updated helps patch vulnerabilities that attackers might exploit.
Database Activity Monitoring
Continuous monitoring helps detect suspicious activities such as unusual login attempts or large data transfers.
Strong Authentication Methods
Implementing multi-factor authentication (MFA) adds an extra layer of protection against unauthorized access.
Backup and Recovery Plans
Regular backups ensure that data can be restored quickly in case of cyberattacks, corruption, or system failures.
Security Audits and Testing
Routine vulnerability assessments and penetration testing help identify potential weaknesses before attackers exploit them.
Future Trends in Database Security
As cyber threats become more sophisticated, database security strategies continue to evolve. Some emerging trends include:
- AI-powered threat detection for identifying unusual database activity
- Zero Trust security models that verify every access request
- Automated compliance monitoring for regulatory requirements
- Cloud database security solutions for protecting distributed data environments
Organizations must stay updated with these advancements to maintain strong security defenses.