Network Security: Protecting Digital Communication in a Connected World
In today’s digital-first environment, computer networks are the backbone of communication, business operations, and data exchange. Organizations rely on networks to connect devices, share information, and access cloud services. However, as networks expand and become more complex, they also become vulnerable to cyber threats.
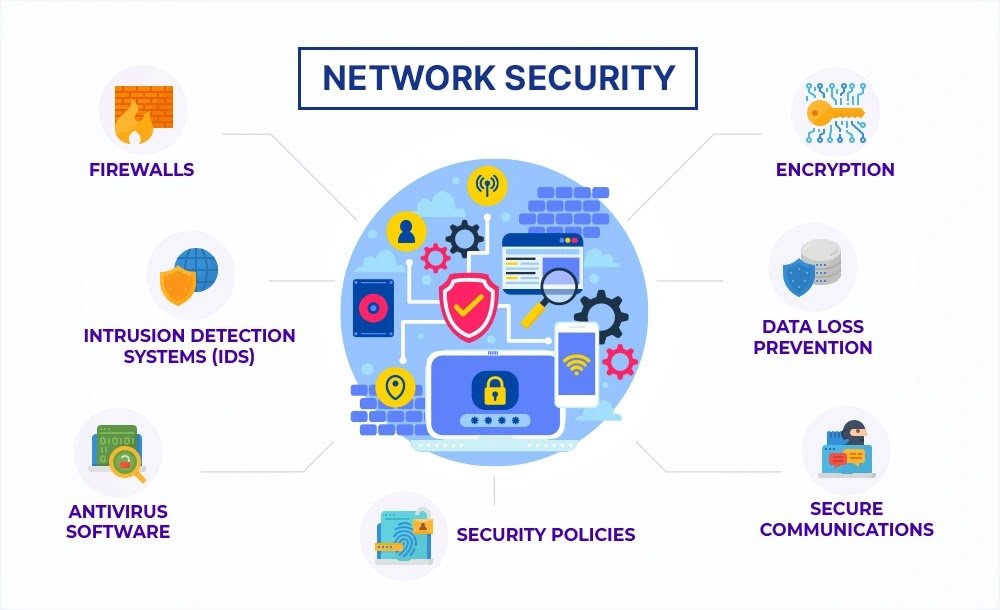
Network Security focuses on protecting both internal and external network communications from unauthorized access, cyberattacks, and data breaches. It includes a combination of technologies, policies, and practices designed to secure network infrastructure and ensure safe data transmission.
Without strong network security measures, organizations risk exposing sensitive data, disrupting operations, and facing financial losses.
Why Network Security Is Important
Modern networks connect employees, customers, partners, and devices across different locations. While this connectivity improves efficiency and collaboration, it also increases the attack surface for cybercriminals.
Hackers often target networks to intercept data, spread malware, or gain access to internal systems. Once inside a network, attackers can move laterally, accessing sensitive systems and causing significant damage.
Network security helps organizations:
- Protect data during transmission
- Prevent unauthorized access to network resources
- Detect and respond to threats quickly
- Maintain business continuity
- Ensure compliance with security regulations
With the rise of remote work and cloud computing, securing network communication has become more critical than ever.
Key Components of Network Security
1. Firewalls
A firewall is a fundamental component of network security. It acts as a barrier between trusted internal networks and untrusted external networks such as the internet.
Firewalls monitor and filter network traffic based on predefined security rules. They block unauthorized access while allowing legitimate communication.
Modern firewalls provide advanced capabilities such as:
- Deep packet inspection
- Application-level filtering
- Threat detection and prevention
- Traffic monitoring and logging
Firewalls are essential for protecting networks from external threats.
2. Intrusion Detection and Prevention Systems (IDS/IPS)
Intrusion Detection Systems (IDS) and Intrusion Prevention Systems (IPS) help identify and respond to suspicious activity within a network.
An IDS monitors network traffic and alerts administrators when potential threats are detected. An IPS goes a step further by automatically blocking malicious activity in real time.
These systems help detect:
- Malware communication
- Unauthorized access attempts
- Network scanning activities
- Exploits targeting vulnerabilities
IDS/IPS solutions provide an additional layer of security beyond firewalls.
3. Network Segmentation
Network segmentation involves dividing a network into smaller, isolated segments. Each segment has its own security controls and access policies.
For example, sensitive systems such as financial databases can be placed in a restricted segment separate from general user networks.
Benefits of network segmentation include:
- Limiting the spread of cyberattacks
- Enhancing access control
- Improving network performance
- Simplifying monitoring and management
Segmentation ensures that even if one part of the network is compromised, attackers cannot easily access other areas.
4. Secure Wi-Fi and VPNs
Wireless networks provide flexibility but can introduce security risks if not properly protected. Unsecured Wi-Fi networks can allow attackers to intercept data or gain unauthorized access.
To secure Wi-Fi networks, organizations should use strong encryption protocols such as WPA3 and implement secure authentication methods.
Virtual Private Networks (VPNs) add another layer of security by encrypting internet connections. VPNs create secure tunnels between users and networks, protecting data from interception.
VPNs are especially important for remote workers who need secure access to corporate systems from different locations.
Common Network Security Threats
Networks face various cyber threats that can compromise security:
Malware Attacks
Malicious software spreads across networks to steal data or disrupt systems.
Distributed Denial of Service (DDoS) Attacks
Attackers overwhelm networks with traffic, causing service outages.
Man-in-the-Middle Attacks
Hackers intercept communication between users and systems.
Unauthorized Access
Weak authentication allows attackers to enter networks.
Understanding these threats helps organizations implement effective defenses.
Best Practices for Strengthening Network Security
Organizations can improve network security by following these best practices:
- Implement firewalls and IDS/IPS systems
- Use strong authentication and access controls
- Segment networks to protect critical assets
- Secure Wi-Fi networks with encryption
- Use VPNs for remote access
- Monitor network traffic continuously
- Conduct regular security audits and vulnerability assessments
A layered security approach provides better protection against evolving threats.