IoT Security: Protecting Connected Devices from Cyber Threats
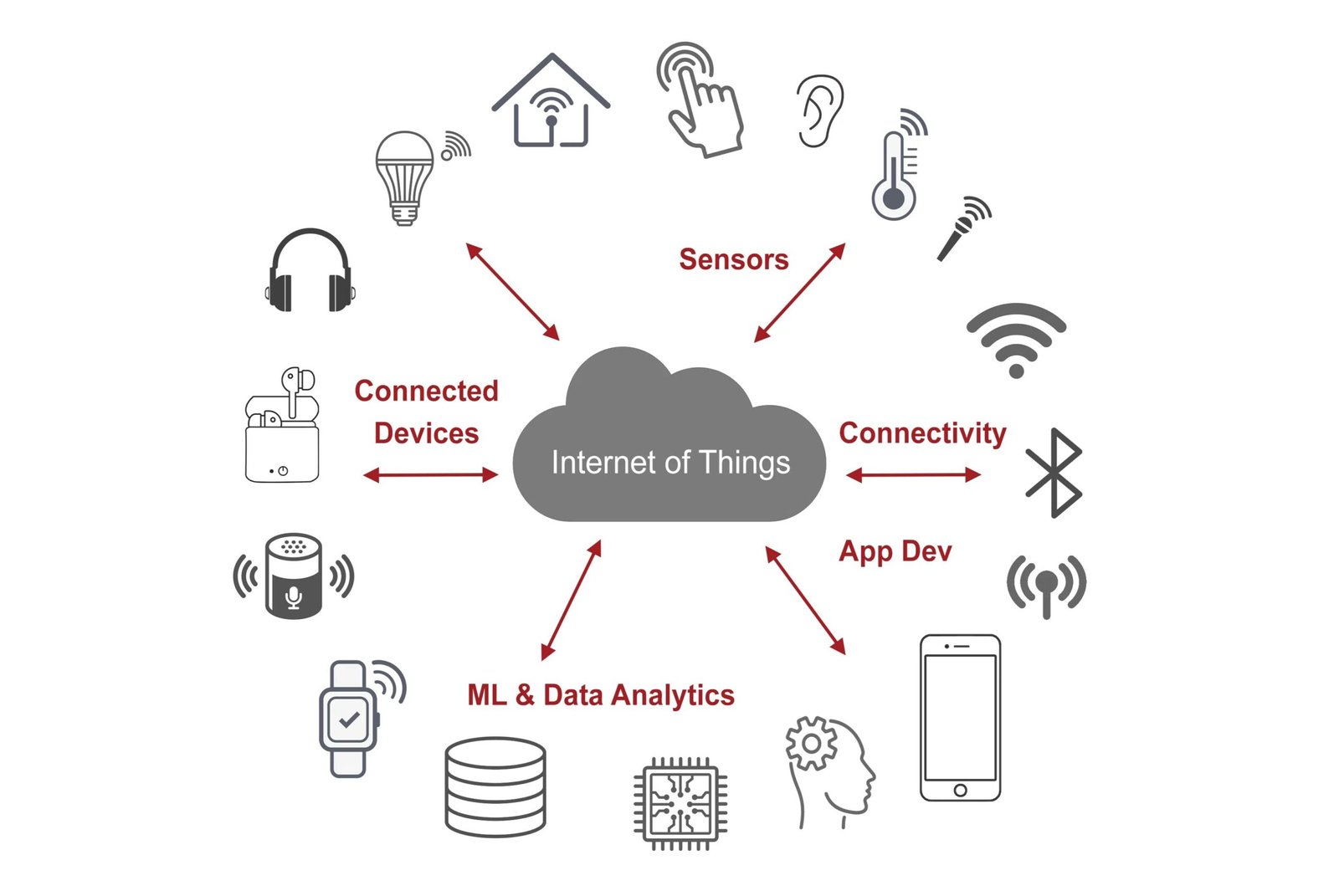
The Internet of Things (IoT) has transformed how we interact with technology. From smart home systems and wearable devices to connected industrial machines, IoT has made life more efficient, automated, and convenient. However, this rapid growth in connected devices has also created new cybersecurity challenges.
IoT Security focuses on protecting internet-connected devices and their networks from unauthorized access, cyberattacks, and data breaches. As billions of devices continue to connect online, securing them has become a critical priority for individuals, businesses, and governments.
Without proper security measures, IoT devices can become easy targets for cybercriminals.
Why IoT Security Is Important
IoT devices are used across multiple sectors, including homes, healthcare, manufacturing, transportation, and smart cities. These devices collect, process, and transmit large amounts of data.
For example:
- Smart home devices manage lighting, cameras, and locks
- Wearables track health and fitness data
- Industrial IoT devices monitor machinery and operations
If these devices are compromised, attackers may gain access to sensitive personal data, disrupt critical operations, or use devices to launch larger cyberattacks.
A single vulnerable device can expose an entire network. This is why IoT security is essential for protecting both privacy and operational continuity.
Types of IoT Devices That Need Protection
1. Smart Home Devices
Smart home technology includes devices such as smart speakers, thermostats, security cameras, smart locks, and home automation systems.
While these devices offer convenience, they often face security risks such as:
- Weak default passwords
- Unpatched firmware vulnerabilities
- Insecure Wi-Fi connections
To secure smart home devices, users should change default passwords, enable multi-factor authentication, and keep firmware updated.
2. Wearable Devices
Wearables such as smartwatches and fitness trackers collect personal health and activity data. This information can include heart rate, sleep patterns, location tracking, and daily activity levels.
Because wearables store sensitive data, attackers may target them to steal personal information or compromise connected mobile applications.
Manufacturers should implement:
- Secure data encryption
- Secure Bluetooth communication
- Strong authentication protocols
Users should also use trusted apps and keep software up to date.
3. Connected Industrial Machines
Industrial IoT (IIoT) devices are used in factories, energy systems, transportation, and supply chains. These devices help automate operations and improve efficiency.
However, industrial machines often connect to critical infrastructure systems. If compromised, attackers can disrupt operations, damage equipment, or affect public services.
Organizations should secure industrial IoT devices by:
Applying regular security updates
Segmenting networks
Using strong access controls
Continuously monitoring system activity
Applying regular security updates
Common IoT Security Threats
IoT environments face several common threats:
Device Hijacking
Attackers take control of devices remotely.
Data Theft
Sensitive data transmitted by devices is intercepted.
Botnet Attacks
Compromised devices are used in large-scale attacks such as DDoS.
Firmware Vulnerabilities
Outdated device software can expose security weaknesses.
Understanding these risks helps organizations implement stronger defenses.
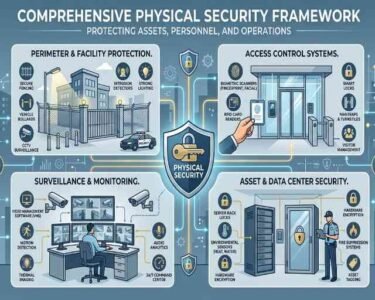
Best Practices for Strengthening IoT Security
To improve IoT security, organizations and users should follow best practices such as:
- Use strong passwords and authentication
- Regularly update firmware and software
- Encrypt device communications
- Separate IoT devices from critical networks
- Monitor device behavior for unusual activity
- Buy devices from trusted manufacturers
These steps help reduce vulnerabilities and improve overall device security.
Future of IoT Security
As IoT adoption continues to grow, new security technologies are emerging to address evolving threats.
Some key trends include:
- AI-powered threat detection
- Zero Trust security frameworks
- Blockchain-based device authentication
- Automated security monitoring tools
These innovations are helping create safer and more resilient IoT ecosystems.