Cloud computing has become the foundation of modern digital infrastructure, enabling organizations to scale rapidly, reduce costs, and innovate faster. However, as businesses increasingly move their data, applications, and services to the cloud, security has emerged as a top concern. In 2026, cloud security is not just an IT priority—it’s a business necessity.
Cloud security focuses on protecting cloud-based systems, data, and infrastructure from cyber threats, unauthorized access, and data breaches. Unlike traditional on-premises environments, cloud environments are dynamic, distributed, and often shared across multiple users, making security more complex.
Why Cloud Security Is Critical Today
The adoption of cloud platforms—whether public, private, or hybrid—has significantly increased the attack surface. Misconfigured cloud settings, weak access controls, and insecure APIs are among the leading causes of cloud breaches.
One of the biggest misconceptions is that cloud providers are solely responsible for security. In reality, cloud security follows a shared responsibility model, where providers secure the infrastructure while customers are responsible for securing their data, applications, and configurations.
Failure to implement proper security measures can lead to data leaks, compliance violations, and financial losses.
Identity and Access Management (IAM): Controlling Who Gets Access
Identity and Access Management (IAM) is a cornerstone of cloud security. It ensures that only authorized users and systems can access specific resources.
Effective IAM practices include:
- Implementing the principle of least privilege (PoLP)
- Using multi-factor authentication (MFA)
- Regularly reviewing and updating access permissions
- Avoiding the use of shared accounts
By tightly controlling access, organizations can significantly reduce the risk of unauthorized activities and insider threats.
Cloud Encryption: Protecting Data at All Times
Encryption is essential for safeguarding sensitive data in the cloud. It ensures that even if data is intercepted or accessed without authorization, it remains unreadable.
There are two primary types of encryption in cloud environments:
- Data at rest – Protects stored data in databases and storage systems
- Data in transit – Secures data as it moves between systems
Organizations should use strong encryption standards and manage encryption keys securely. Many cloud providers offer built-in encryption services, but proper configuration is crucial.
Monitoring and Threat Detection
Continuous monitoring is vital for detecting and responding to security incidents in real time. Cloud environments generate vast amounts of logs and data, which can be analyzed to identify suspicious activities.
Security tools such as Security Information and Event Management (SIEM) systems and cloud-native monitoring solutions help organizations:
- Detect unusual login attempts
- Identify misconfigurations
- Monitor network traffic
- Respond to potential breaches quickly
Automation and artificial intelligence are increasingly being used to enhance threat detection and response capabilities.
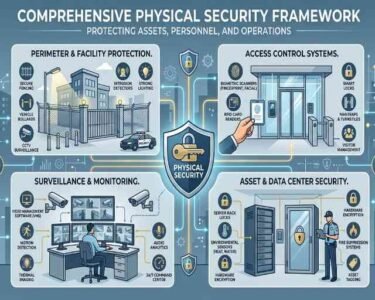
Securing Cloud Infrastructure
Cloud infrastructure must be configured securely to prevent vulnerabilities. Misconfigurations—such as publicly exposed storage buckets or open ports—are among the most common causes of breaches.
Best practices for securing cloud infrastructure include:
Implementing network security controls like firewalls and private networks
Regular security audits and configuration reviews
Using infrastructure-as-code (IaC) with security checks
Keeping systems and applications updated
Adopting a “security by design” approach ensures that security is integrated into every stage of cloud deployment.
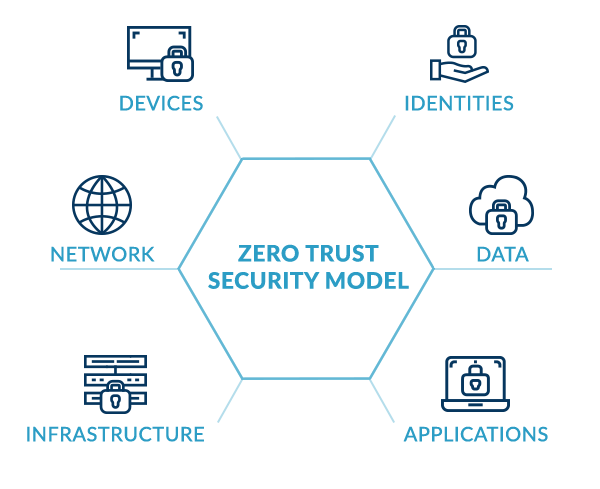
The Rise of Zero Trust in the Cloud
Zero Trust Architecture (ZTA) is becoming a key strategy in cloud security. Instead of trusting users or systems by default, Zero Trust requires continuous verification of every access request.
This approach is particularly effective in cloud environments, where users access resources from different locations and devices. By enforcing strict authentication and monitoring, Zero Trust minimizes the risk of unauthorized access.
Compliance and Data Privacy
With increasing regulations around data protection, organizations must ensure that their cloud environments comply with legal and industry standards. This includes implementing proper data handling practices, maintaining audit logs, and ensuring transparency in data usage.
Compliance is not just about avoiding penalties—it also builds trust with customers and stakeholders.
Final Thoughts
Cloud security is an ongoing journey that requires a proactive and comprehensive approach. As cyber threats continue to evolve, organizations must stay ahead by implementing strong access controls, encryption, monitoring, and secure configurations.
In 2026, successful businesses are those that embrace cloud technology without compromising security. By understanding the shared responsibility model and adopting best practices, organizations can protect their digital assets and confidently navigate the cloud-first world.